At Semgrep, we're passionate about finding and fixing security issues in code. When GPT was released, we jumped to experiment with it; we asked ourselves, could it help improve Semgrep for the developer community? While generative AI is still a developing technology, our preliminary results have been impressive, and worthy of sharing in our first AI-augmented beta: Semgrep Assistant.
Semgrep Assistant uses GPT to make triage suggestions (i.e., label true positives) and provide automatic code fixes, all within pull requests. The early results are promising, and we invite you to experiment with AI-augmented Semgrep: join the waitlist for the private beta.
Areas where we are experimenting with GPT-4
Using AI for triaging vulnerabilities
Our goal with Semgrep is to maximize the fix rate: the rate of issues developers fix versus what the tool complains about. Before fixing an issue, developers have to decide whether a result is a true positive. We believe that auto-labeling from GPT can reduce a developer's work to reason about a result and improve their confidence in the finding. GPT is valuable because it uses signals beyond Semgrep’s parsing and dataflow engines–some of the most difficult sources of false positives are context outside of what a program analysis engine sees: test code, code that won't be deployed to product, or code that is technically vulnerable but is mitigated by some other configuration setting.
In our testing, we got accurate triage advice that was both insightful and reduced our work by deciding to fix or ignore a finding.
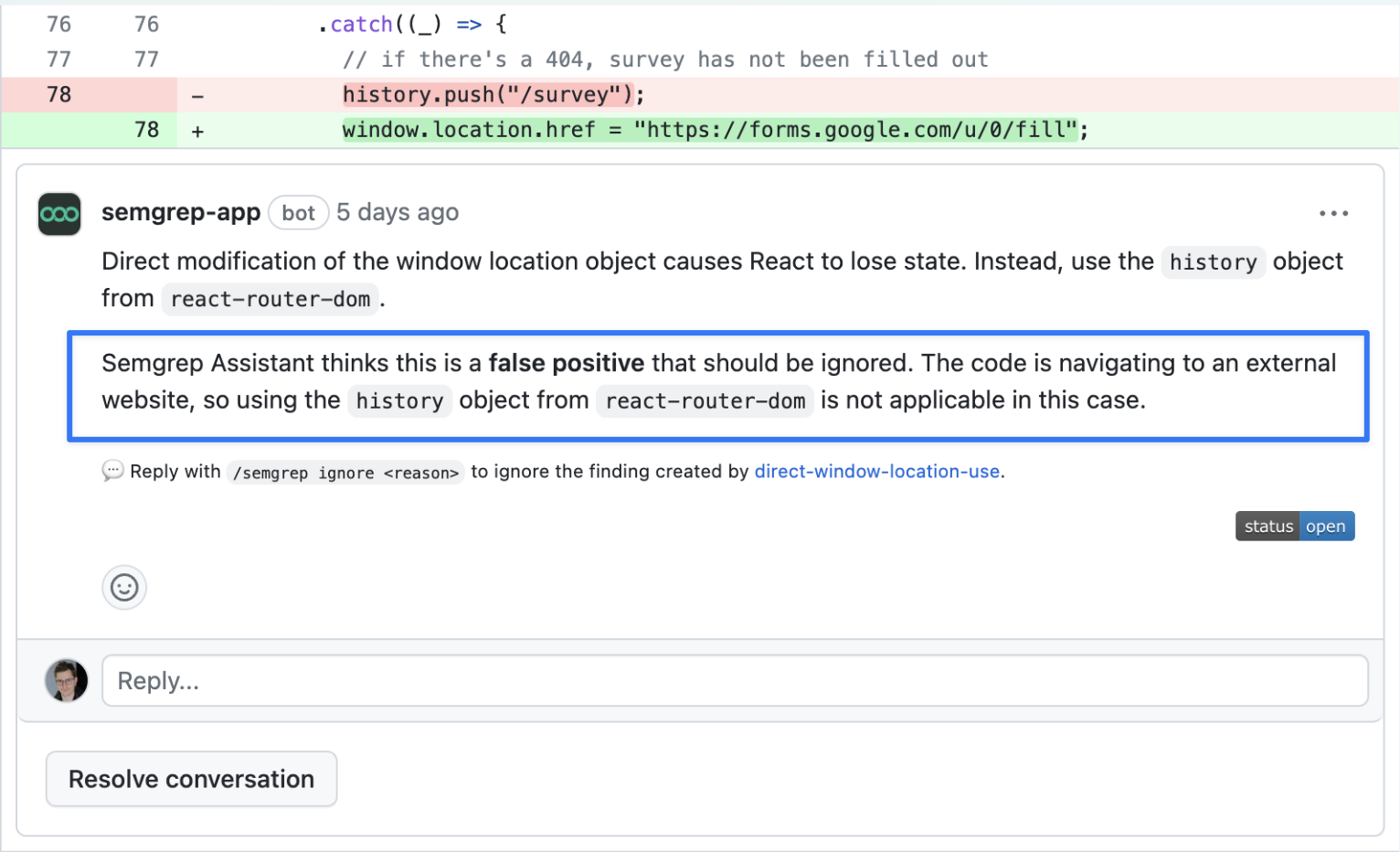 Figure 1: Semgrep Assistant suggests a false positive label with rationale
Figure 1: Semgrep Assistant suggests a false positive label with rationale
Using AI for fixing insecure code
Another avenue to improve the fix rate is to make it easier to fix issues by providing tailored code-change suggestions. You can already use auto fixes that are specified in the Semgrep rule syntax, but most rule authors don’t include them. We want to increase the percentage of time Semgrep provides detailed and specific remediation advice for your code. This inline guidance saves developer time searching the internet, pinging internal security experts, or typing out the solution.
Prompting GPT with the information Semgrep has (vulnerability information, the vulnerable code, CVE identifiers), we found that it can produce accurate and acceptable remediation suggestions! This is extremely exciting because Semgrep can detect the problem and we can now suggest solutions for most results. Ultimately, it’s a suggestion and it’s up to the engineer to accept it or not. Figure 2: Semgrep Assistant suggests a fix for a developer-focused issue
Figure 2: Semgrep Assistant suggests a fix for a developer-focused issue
Using AI for writing custom rules
Several months ago on the Semgrep Slack, multiple community members shared that ChatGPT was quite good at writing Semgrep rules.
 Figure 3: An example of Semgrep Community members writing custom rules using ChatGPT
Figure 3: An example of Semgrep Community members writing custom rules using ChatGPT
The Semgrep engine is built entirely around the concept of comprehending patterns and rules. Rules are YAML instructions that Semgrep employs to detect patterns in code, similar to writing unit tests. Rules can be created, removed, modified, or even custom-made by anyone. This allows the results to be fine-tuned to fit your needs perfectly, setting Semgrep apart from similar products.
But even though writing rules via YAML is relatively simple, you still need to learn how to write them. The good news is that GPT is really good at writing code in many full-fledged programming languages, and Semgrep rules are actually a simpler form of a full-fledged programming language. Using GPT to automatically write or update custom rules for everyone doesn’t need to be perfect; even if it gets people halfway there, that by itself is hugely valuable.
We are still in the early stages of experimenting with this, and if it meets our expectations, we’ll provide more details about it. Watch this space.
If this sounds as exciting to you as it does to us, join the waitlist so you can try Semgrep Assistant for yourself. By joining the waitlist, you can also send feedback and join private Slack channels.


.jpg)
